- Home
- Bruce Sterling
GURPS' LABOUR LOST
GURPS' LABOUR LOST Read online
GURPS’ LABOUR LOST
Bruce Sterling
Bruce Sterling
GURPS’ LABOUR LOST
Some months ago, I wrote an article about the raid on Steve Jackson Games, which appeared in my “Comment” column in the British science fiction monthly, INTERZONE (#44, Feb 1991). This updated version, specially re-written for dissemination by EFF, reflects the somewhat greater knowledge I’ve gained to date, in the course of research on an upcoming nonfiction book, THE HACKER CRACKDOWN: Law and Disorder on the Electronic Frontier.
The bizarre events suffered by Mr. Jackson and his co-workers, in my own home town of Austin, Texas, were directly responsible for my decision to put science fiction aside and to tackle the purportedly real world of computer crime and electronic free-expression.
The national crackdown on computer hackers in 1990 was the largest and best-coordinated attack on computer mischief in American history. There was Arizona’s “Operation Sundevil,” the sweeping May 8 nationwide raid against outlaw bulletin boards. The BellSouth E911 case (of which the Jackson raid was a small and particularly egregious part) was coordinated out of Chicago. The New York State Police were also very active in 1990.
All this vigorous law enforcement activity meant very little to the narrow and intensely clannish world of science fiction. All we knew — and this misperception persisted, uncorrected, for months — was that Mr. Jackson had been raided because of his intention to publish a gaming book about “cyberpunk” science fiction. The Jackson raid received extensive coverage in science fiction news magazines (yes, we have these) and became notorious in the world of SF as “the Cyberpunk Bust.” My INTERZONE article attempted to make the Jackson case intelligible to the British SF audience.
What possible reason could lead an American federal law enforcement agency to raid the headquarters of a science-fiction gaming company? Why did armed teams of city police, corporate security men, and federal agents roust two Texan computer-hackers from their beds at dawn, and then deliberately confiscate thousands of dollars’ worth of computer equipment, including the hackers’ common household telephones? Why was an unpublished book called G.U.R.P.S. Cyberpunk seized by the US Secret Service and declared “a manual for computer crime?” These weird events were not parodies or fantasies; no, this was real.
The first order of business in untangling this bizarre drama is to understand the players — who come in entire teams.
Dramatis Personae
PLAYER ONE: The Law Enforcement Agencies.
America’s defense against the threat of computer crime is a confusing hodgepodge of state, municipal, and federal agencies. Ranked first, by size and power, are the Central Intelligence Agency (CIA), the National Security Agency (NSA), and the Federal Bureau of Investigation (FBI), large, potent and secretive organizations who, luckily, play almost no role in the Jackson story.
The second rank of such agencies include the Internal Revenue Service (IRS), the National Aeronatics and Space Administration (NASA), the Justice Department, the Department of Labor, and various branches of the defense establishment, especially the Air Force Office of Special Investigations (AFOSI). Premier among these groups, however, is the highly-motivated US Secret Service (USSS), best-known to Britons as the suited, mirrorshades-toting, heavily-armed bodyguards of the President of the United States.
Guarding high-ranking federal officials and foreign dignitaries is a hazardous, challenging and eminently necessary task, which has won USSS a high public profile. But Abraham Lincoln created this oldest of federal law enforcement agencies in order to foil counterfeiting. Due to the historical tribulations of the Treasury Department (of which USSS is a part), the Secret Service also guards historical documents, analyzes forgeries, combats wire fraud, and battles “computer fraud and abuse.” These may seem unrelated assignments, but the Secret Service is fiercely aware of its duties. It is also jealous of its bureaucratic turf, especially in computer-crime, where it formally shares jurisdiction with its traditional rival, the johnny-come-lately FBI.
As the use of plastic money has spread, and their long-established role as protectors of the currency has faded in importance, the Secret Service has moved aggressively into the realm of electronic crime. Unlike the lordly NSA, CIA, and FBI, which generally can’t be bothered with domestic computer mischief, the Secret Service is noted for its street-level enthusiasm.
The third-rank of law enforcement are the local “dedicated computer crime units.” There are very few such groups, pitifully undermanned. They struggle hard for their funding and the vital light of publicity. It’s difficult to make white-collar computer crimes seem pressing, to an American public that lives in terror of armed and violent street-crime.
These local groups are small — often, one or two officers, computer hobbyists, who have drifted into electronic crimebusting because they alone are game to devote time and effort to bringing law to the electronic frontier. California’s Silicon Valley has three computer-crime units. There are others in Florida, Illinois, Ohio, Maryland, Texas, Colorado, and a formerly very active one in Arizona — all told, though, perhaps only fifty people nationwide.
The locals do have one great advantage, though. They all know one another. Though scattered across the country, they are linked by both public-sector and private-sector professional societies, and have a commendable subcultural esprit-de-corps. And in the well-manned Secret Service, they have willing national-level assistance.
PLAYER TWO: The Telephone Companies.
In the early 80s, after years of bitter federal court battle, America’s telephone monopoly was pulverized. “Ma Bell,” the national phone company, became AT&T, AT&T Industries, and the regional “Baby Bells,” all purportedly independent companies, who compete with new communications companies and other long-distance providers. As a class, however, they are all sorely harassed by fraudsters, phone phreaks, and computer hackers, and they all maintain computer-security experts. In a lot of cases these “corporate security divisions” consist of just one or two guys, who drifted into the work from backgrounds in traditional security or law enforcement. But, linked by specialized security trade journals and private sector trade groups, they all know one another.
PLAYER THREE: The Computer Hackers.
The American “hacker” elite consists of about a hundred people, who all know one another. These are the people who know enough about computer intrusion to baffle corporate security and alarm police (and who, furthermore, are willing to put their intrusion skills into actual practice). The somewhat older subculture of “phone-phreaking,” once native only to the phone system, has blended into hackerdom as phones have become digital and computers have been netted-together by telephones. “Phone phreaks,” always tarred with the stigma of rip-off artists, are nowadays increasingly hacking PBX systems and cellular phones. These practices, unlike computer-intrusion, offer direct and easy profit to fraudsters.
There are legions of minor “hackers,” such as the “kodez kidz,” who purloin telephone access codes to make free (i.e., stolen) phone calls. Code theft can be done with home computers, and almost looks like real “hacking,” though “kodez kidz” are regarded with lordly contempt by the elite. “Warez d00dz,” who copy and pirate computer games and software, are a thriving subspecies of “hacker,” but they played no real role in the crackdown of 1990 or the Jackson case. As for the dire minority who create computer viruses, the less said the better.
The princes of hackerdom skate the phone-lines, and computer networks, as a lifestyle. They hang out in loose, modem-connected gangs like the “Legion of Doom” and the “Masters of Destruction.” The craft of hacking is taught through “bulletin board systems,” personal computers that carry electronic mail and
can be accessed by phone. Hacker bulletin boards generally sport grim, scary, sci-fi heavy metal names like BLACK ICE — PRIVATE or SPEED DEMON ELITE. Hackers themselves often adopt romantic and highly suspicious tough-guy monickers like “Necron 99,” “Prime Suspect,” “Erik Bloodaxe,” “Malefactor” and “Phase Jitter.” This can be seen as a kind of cyberpunk folk-poetry — after all, baseball players also have colorful nicknames. But so do the Mafia and the Medellin Cartel.
PLAYER FOUR: The Simulation Gamers.
Wargames and role-playing adventures are an old and honored pastime, much favored by professional military strategists and H.G. Wells, and now played by hundreds of thousands of enthusiasts throughout North America, Europe and Japan. In today’s market, many simulation games are computerized, making simulation gaming a favorite pastime of hackers, who dote on arcane intellectual challenges and the thrill of doing simulated mischief.
Modern simulation games frequently have a heavily science-fictional cast. Over the past decade or so, fueled by very respectable royalties, the world of simulation gaming has increasingly permeated the world of science-fiction publishing. TSR, Inc., proprietors of the best-known role-playing game, “Dungeons and Dragons,” own the venerable science-fiction magazine “Amazing.” Gaming-books, once restricted to hobby outlets, now commonly appear in chain-stores like B. Dalton’s and Waldenbooks, and sell vigorously.
Steve Jackson Games, Inc., of Austin, Texas, is a games company of the middle rank. In early 1990, it employed fifteen people. In 1989, SJG grossed about half a million dollars. SJG’s Austin headquarters is a modest two-story brick office-suite, cluttered with phones, photocopiers, fax machines and computers. A publisher’s digs, it bustles with semi-organized activity and is littered with glossy promotional brochures and dog-eared SF novels. Attached to the offices is a large tin-roofed warehouse piled twenty feet high with cardboard boxes of games and books. This building was the site of the “Cyberpunk Bust.”
A look at the company’s wares, neatly stacked on endless rows of cheap shelving, quickly shows SJG’s long involvement with the Science Fiction community. SJG’s main product, the Generic Universal Role-Playing System or G.U.R.P.S., features licensed and adapted works from many genre writers. There is GURPS Witch World, GURPS Conan, GURPS Riverworld, GURPS Horseclans, many names eminently familiar to SF fans. (GURPS Difference Engine is currently in the works.) GURPS Cyberpunk, however, was to be another story entirely.
PLAYER FIVE: The Science Fiction Writers.
The “cyberpunk” SF writers are a small group of mostly college-educated white litterateurs, without conspicuous criminal records, scattered through the US and Canada. Only one, Rudy Rucker, a professor of computer science in Silicon Valley, would rank with even the humblest computer hacker. However, these writers all own computers and take an intense, public, and somewhat morbid interest in the social ramifications of the information industry. Despite their small numbers, they all know one another, and are linked by antique print-medium publications with unlikely names like SCIENCE FICTION EYE, ISAAC ASIMOV’S SCIENCE FICTION MAGAZINE, OMNI and INTERZONE.
PLAYER SIX: The Civil Libertarians.
This small but rapidly growing group consists of heavily politicized computer enthusiasts and heavily cyberneticized political activists: a mix of wealthy high-tech entrepreneurs, veteran West Coast troublemaking hippies, touchy journalists, and toney East Coast civil rights lawyers. They are all getting to know one another.
We now return to our story. By 1988, law enforcement officials, led by contrite teenage informants, had thoroughly permeated the world of underground bulletin boards, and were alertly prowling the nets compiling dossiers on wrongdoers. While most bulletin board systems are utterly harmless, some few had matured into alarming reservoirs of forbidden knowledge. One such was BLACK ICE — PRIVATE, located “somewhere in the 607 area code,” frequented by members of the “Legion of Doom” and notorious even among hackers for the violence of its rhetoric, which discussed sabotage of phone-lines, drug-manufacturing techniques, and the assembly of home-made bombs, as well as a plethora of rules-of-thumb for penetrating computer security.
Of course, the mere discussion of these notions is not illegal — many cyberpunk SF stories positively dote on such ideas, as do hundreds of spy epics, techno-thrillers and adventure novels. It was no coincidence that “ICE,” or “Intrusion Countermeasures Electronics,” was a term invented by cyberpunk writer Tom Maddox, and “BLACK ICE,” or a computer-defense that fries the brain of the unwary trespasser, was a coinage of William Gibson.
A reference manual from the US National Institute of Justice, “Dedicated Computer Crime Units” by J. Thomas McEwen, suggests that federal attitudes toward bulletin-board systems are ambivalent at best:
“There are several examples of how bulletin boards have been used in support of criminal activities…. (B)ulletin boards were used to relay illegally obtained access codes into computer service companies. Pedophiles have been known to leave suggestive messages on bulletin boards, and other sexually oriented messages have been found on bulletin boards. Members of cults and sects have also communicated through bulletin boards. While the storing of information on bulletin boards may not be illegal, the use of bulletin boards has certainly advanced many illegal activities.”
Here is a troubling concept indeed: invisible electronic pornography, to be printed out at home and read by sects and cults. It makes a mockery of the traditional law-enforcement techniques concerning the publication and prosecution of smut. In fact, the prospect of large numbers of antisocial conspirators, congregating in the limbo of cyberspace without official oversight of any kind, is enough to trouble the sleep of anyone charged with maintaining public order.
Even the sternest free-speech advocate will likely do some headscratching at the prospect of digitized “anarchy files” teaching lock-picking, pipe-bombing, martial arts techniques, and highly unorthodox uses for shotgun shells, especially when these neat-o temptations are distributed freely to any teen (or pre-teen) with a modem.
These may be largely conjectural problems at present, but the use of bulletin boards to foment hacker mischief is real. Worse yet, the bulletin boards themselves are linked, sharing their audience and spreading the wicked knowledge of security flaws in the phone network, and in a wide variety of academic, corporate and governmental computer systems.
This strength of the hackers is also a weakness, however. If the boards are monitored by alert informants and/or officers, the whole wicked tangle can be seized all along its extended electronic vine, rather like harvesting pumpkins.
The war against hackers, including the “Cyberpunk Bust,” was primarily a war against hacker bulletin boards. It was, first and foremost, an attack against the enemy’s means of information.
This basic strategic insight supplied the tactics for the crackdown of 1990. The variant groups in the national subculture of cyber-law would be kept apprised, persuaded to action, and diplomatically martialled into effective strike position. Then, in a burst of energy and a glorious blaze of publicity, the whole nest of scofflaws would be wrenched up root and branch. Hopefully, the damage would be permanent; if not, the swarming wretches would at least keep their heads down.
“Operation Sundevil,” the Phoenix-inspired crackdown of May 8,1990, concentrated on telephone code-fraud and credit-card abuse, and followed this seizure plan with some success. Boards went down all over America, terrifying the underground and swiftly depriving them of at least some of their criminal instruments. It also saddled analysts with some 24,000 floppy disks, and confronted harried Justice Department prosecutors with the daunting challenge of a gigantic nationwide hacker show-trial involving highly technical issues in dozens of jurisdictions. As of July 1991, it must be questioned whether the climate is right for an action of this sort, especially since several of the most promising prosecutees have already been jailed on other charges.
“Sundevil” aroused many dicey legal and constitutional
questions, but at least its organizers were spared the spectacle of seizure victims loudly proclaiming their innocence — (if one excepts Bruce Esquibel, sysop of “Dr. Ripco,” an anarchist board in Chicago).
The activities of March 1, 1990, however, including the Jackson case, were the inspiration of the Chicago-based Computer Fraud and Abuse Task Force. At telco urging, the Chicago group were pursuing the purportedly vital “E911 document” with headlong energy. As legal evidence, this proprietary Bell South document was to prove a very weak reed in the Craig Neidorf trial, which ended in a humiliating dismissal and a triumph for Neidorf. As of March 1990, however, this purloined data-file seemed a red-hot chunk of contraband, and the decision was made to track it down wherever it might have gone, and to shut down any board that had touched it — or even come close to it.
In the meantime, however — early 1990 — Mr. Loyd Blankenship, an employee of Steve Jackson Games, an accomplished hacker, and a sometime member and file-writer for the Legion of Doom, was contemplating a “cyberpunk” simulation-module for the flourishing GURPS gaming-system.
The time seemed ripe for such a product, which had already been proven in the marketplace. The first games-company out of the gate, with a product boldly called “Cyberpunk” in defiance of possible infringement-of-copyright suits, had been an upstart group called R. Talsorian. Talsorian’s “Cyberpunk” was a fairly decent game, but the mechanics of the simulation system sucked, and the nerds who wrote the manual were the kimd of half-hip twits who wrote their own fake rock lyrics and, worse yet, published them. The game sold like crazy, though.
The next “cyberpunk” game had been the even more successful “Shadowrun” by FASA Corporation. The mechanics of this game were fine, but the scenario was rendered moronic by lame fantasy elements like orcs, dwarves, trolls, magicians, and dragons — all highly ideologically-incorrect, according to the hard-edged, high-tech standards of cyberpunk science fiction. No true cyberpunk fan could play this game without vomiting, despite FASA’s nifty T-shirts and street-samurai lead figurines.

 Mirrorshades: The Cyberpunk Anthology
Mirrorshades: The Cyberpunk Anthology The Wonderful Power of Storytelling
The Wonderful Power of Storytelling Love Is Strange (A Paranormal Romance)
Love Is Strange (A Paranormal Romance) Globalhead
Globalhead Essays. FSF Columns
Essays. FSF Columns The Hacker Crackdown
The Hacker Crackdown Bicycle Repairman
Bicycle Repairman Black Swan
Black Swan Crystal Express
Crystal Express Islands in the Net
Islands in the Net Pirate Utopia
Pirate Utopia GURPS' LABOUR LOST
GURPS' LABOUR LOST The Dead Media Notebook
The Dead Media Notebook Unstable Networks
Unstable Networks The Manifesto of January 3, 2000
The Manifesto of January 3, 2000 Heavy Weather
Heavy Weather Involution Ocean
Involution Ocean The Epic Struggle of the Internet of Things
The Epic Struggle of the Internet of Things A Good Old-Fashioned Future
A Good Old-Fashioned Future The Littlest Jackal
The Littlest Jackal Zeitgeist
Zeitgeist Totem Poles
Totem Poles Ascendancies
Ascendancies CyberView 1991
CyberView 1991 War Is Virtual Hell
War Is Virtual Hell Taklamakan
Taklamakan Holy Fire
Holy Fire Cyberpunk in the Nineties
Cyberpunk in the Nineties Schismatrix Plus
Schismatrix Plus The Artificial Kid
The Artificial Kid Essays. Catscan Columns
Essays. Catscan Columns Maneki Neko
Maneki Neko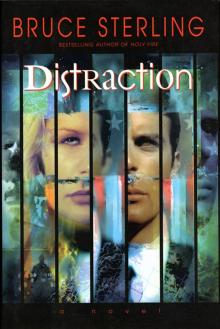 Distraction
Distraction In Paradise
In Paradise Red Star, Winter Orbit
Red Star, Winter Orbit Luciferase
Luciferase