- Home
- Bruce Sterling
The Hacker Crackdown
The Hacker Crackdown Read online
The Hacker Crackdown
Bruce Sterling
Bruce Sterling
The Hacker Crackdown
Hi, I'm Bruce Sterling, the author of this electronic book.
Out in the traditional world of print, *The Hacker Crackdown* is ISBN 0-553-08058-X, and is formally catalogued by the Library of Congress as "1. Computer crimes -- United States. 2. Telephone -- United States -- Corrupt practices. 3. Programming (Electronic computers) -- United States -- Corrupt practices." 'Corrupt practices,' I always get a kick out of that description. Librarians are very ingenious people.
The paperback is ISBN 0-553-56370-X. If you go and buy a print version of *The Hacker Crackdown,* an action I encourage heartily, you may notice that in the front of the book, beneath the copyright notice -- "Copyright (C) 1992 by Bruce Sterling" -- it has this little block of printed legal boilerplate from the publisher. It says, and I quote:
"No part of this book may be reproduced or transmitted in any form or by any means, electronic or mechanical, including photocopying, recording, or by any information storage and retrieval system, without permission in writing from the publisher. For information address: Bantam Books."
This is a pretty good disclaimer, as such disclaimers go. I collect intellectual-property disclaimers, and I've seen dozens of them, and this one is at least pretty straightforward. In this narrow and particular case, however, it isn't quite accurate. Bantam Books puts that disclaimer on every book they publish, but Bantam Books does not, in fact, own the electronic rights to this book. I do, because of certain extensive contract maneuverings my agent and I went through before this book was written. I want to give those electronic publishing rights away through certain not-for-profit channels, and I've convinced Bantam that this is a good idea.
Since Bantam has seen fit to peacably agree to this scheme of mine, Bantam Books is not going to fuss about this. Provided you don't try to sell the book, they are not going to bother you for what you do with the electronic copy of this book. If you want to check this out personally, you can ask them; they're at 1540 Broadway NY NY 10036. However, if you were so foolish as to print this book and start retailing it for money in violation of my copyright and the commercial interests of Bantam Books, then Bantam, a part of the gigantic Bertelsmann multinational publishing combine, would roust some of their heavy-duty attorneys out of hibernation and crush you like a bug. This is only to be expected. I didn't write this book so that you could make money out of it. If anybody is gonna make money out of this book, it's gonna be me and my publisher.
My publisher deserves to make money out of this book. Not only did the folks at Bantam Books commission me to write the book, and pay me a hefty sum to do so, but they bravely printed, in text, an electronic document the reproduction of which was once alleged to be a federal felony. Bantam Books and their numerous attorneys were very brave and forthright about this book. Furthermore, my former editor at Bantam Books, Betsy Mitchell, genuinely cared about this project, and worked hard on it, and had a lot of wise things to say about the manuscript. Betsy deserves genuine credit for this book, credit that editors too rarely get.
The critics were very kind to *The Hacker Crackdown,* and commercially the book has done well. On the other hand, I didn't write this book in order to squeeze every last nickel and dime out of the mitts of impoverished sixteen-year-old cyberpunk high-school-students. Teenagers don't have any money -- (no, not even enough for the six- dollar *Hacker Crackdown* paperback, with its attractive bright-red cover and useful index). That's a major reason why teenagers sometimes succumb to the temptation to do things they shouldn't, such as swiping my books out of libraries. Kids: this one is all yours, all right? Go give the print version back. *8-)
Well-meaning, public-spirited civil libertarians don't have much money, either. And it seems almost criminal to snatch cash out of the hands of America's direly underpaid electronic law enforcement community.
If you're a computer cop, a hacker, or an electronic civil liberties activist, you are the target audience for this book. I wrote this book because I wanted to help you, and help other people understand you and your unique, uhm, problems. I wrote this book to aid your activities, and to contribute to the public discussion of important political issues. In giving the text away in this fashion, I am directly contributing to the book's ultimate aim: to help civilize cyberspace.
Information *wants* to be free. And the information inside this book longs for freedom with a peculiar intensity. I genuinely believe that the natural habitat of this book is inside an electronic network. That may not be the easiest direct method to generate revenue for the book's author, but that doesn't matter; this is where this book belongs by its nature. I've written other books -- plenty of other books -- and I'll write more and I am writing more, but this one is special. I am making *The Hacker Crackdown* available electronically as widely as I can conveniently manage, and if you like the book, and think it is useful, then I urge you to do the same with it.
You can copy this electronic book. Copy the heck out of it, be my guest, and give those copies to anybody who wants them. The nascent world of cyberspace is full of sysadmins, teachers, trainers, cybrarians, netgurus, and various species of cybernetic activist. If you're one of those people, I know about you, and I know the hassle you go through to try to help people learn about the electronic frontier. I hope that possessing this book in electronic form will lessen your troubles. Granted, this treatment of our electronic social spectrum is not the ultimate in academic rigor. And politically, it has something to offend and trouble almost everyone. But hey, I'm told it's readable, and at least the price is right.
You can upload the book onto bulletin board systems, or Internet nodes, or electronic discussion groups. Go right ahead and do that, I am giving you express permission right now. Enjoy yourself.
You can put the book on disks and give the disks away, as long as you don't take any money for it.
But this book is not public domain. You can't copyright it in your own name. I own the copyright. Attempts to pirate this book and make money from selling it may involve you in a serious litigative snarl. Believe me, for the pittance you might wring out of such an action, it's really not worth it. This book don't "belong" to you. In an odd but very genuine way, I feel it doesn't "belong" to me, either. It's a book about the people of cyberspace, and distributing it in this way is the best way I know to actually make this information available, freely and easily, to all the people of cyberspace -- including people far outside the borders of the United States, who otherwise may never have a chance to see any edition of the book, and who may perhaps learn something useful from this strange story of distant, obscure, but portentous events in so-called "American cyberspace."
This electronic book is now literary freeware. It now belongs to the emergent realm of alternative information economics. You have no right to make this electronic book part of the conventional flow of commerce. Let it be part of the flow of knowledge: there's a difference. I've divided the book into four sections, so that it is less ungainly for upload and download; if there's a section of particular relevance to you and your colleagues, feel free to reproduce that one and skip the rest.
Just make more when you need them, and give them to whoever might want them.
Now have fun.
Bruce Sterling -- [email protected]
CHRONOLOGY OF THE HACKER CRACKDOWN
1865 U.S. Secret Service (USSS) founded.
1876 Alexander Graham Bell invents telephone.
1878 First teenage males flung off phone system by enraged authorities.
1939 "Futurian" science-fiction group raided by Secret Service.
1971 Yippie phone phreaks start YIPL/TAP magazi
ne.
1972 *Ramparts* magazine seized in blue-box rip-off scandal.
1978 Ward Christenson and Randy Suess create first personal computer bulletin board system.
1982 William Gibson coins term "cyberspace."
1982 "414 Gang" raided.
1983-1983 AT&T dismantled in divestiture.
1984 Congress passes Comprehensive Crime Control Act giving USSS jurisdiction over credit card fraud and computer fraud.
1984 "Legion of Doom" formed.
1984. *2600: The Hacker Quarterly* founded.
1984. *Whole Earth Software Catalog* published.
1985. First police "sting" bulletin board systems established.
1985. Whole Earth 'Lectronic Link computer conference (WELL) goes on-line.
1986 Computer Fraud and Abuse Act passed.
1986 Electronic Communications Privacy Act passed.
1987 Chicago prosecutors form Computer Fraud and Abuse Task Force.
1988
July. Secret Service covertly videotapes "SummerCon" hacker convention.
September. "Prophet" cracks BellSouth AIMSX computer network and downloads E911 Document to his own computer and to Jolnet.
September. AT&T Corporate Information Security informed of Prophet's action.
October. Bellcore Security informed of Prophet's action.
1989
January. Prophet uploads E911 Document to Knight Lightning.
February 25. Knight Lightning publishes E911Document in *Phrack* electronic newsletter.
May. Chicago Task Force raids and arrests "Kyrie."
June. "NuPrometheus League" distributes Apple Computer proprietary software.
June 13. Florida probation office crossed with phone-sex line in switching-station stunt.
July. "Fry Guy" raided by USSS and Chicago Computer Fraud and Abuse Task Force.
July. Secret Service raids "Prophet," "Leftist," and "Urvile" in Georgia.
1990
January 15. Martin Luther King Day Crash strikes AT&T long-distance network nationwide.
January 18-19 Chicago Task Force raids Knight Lightning in St. Louis.
January 24. USSS and New York State Police raid "Phiber Optik," "Acid Phreak," and "Scorpion" in New York City.
February 1. USSS raids "Terminus" in Maryland.
February 3. Chicago Task Force raids Richard Andrews' home.
February 6. Chicago Task Force raids Richard Andrews' business.
February 6. USSS arrests Terminus, Prophet, Leftist, and Urvile.
February 9. Chicago Task Force arrests Knight Lightning.
February 20. AT&T Security shuts down public-access "attctc" computer in Dallas.
February 21. Chicago Task Force raids Robert Izenberg in Austin.
March 1. Chicago Task Force raids Steve Jackson Games, Inc., "Mentor," and "Erik Bloodaxe" in Austin.
May 7,8,9. USSS and Arizona Organized Crime and Racketeering Bureau conduct "Operation Sundevil" raids in Cincinnatti, Detroit, Los Angeles, Miami, Newark, Phoenix, Pittsburgh, Richmond, Tucson, San Diego, San Jose, and San Francisco.
May. FBI interviews John Perry Barlow re NuPrometheus case.
June. Mitch Kapor and Barlow found Electronic Frontier Foundation; Barlow publishes *Crime and Puzzlement* manifesto.
July 24-27. Trial of Knight Lightning.
1991
February. CPSR Roundtable in Washington, D.C.
March 25-28. Computers, Freedom and Privacy conference in San Francisco.
May 1. Electronic Frontier Foundation, Steve Jackson, and others file suit against members of Chicago Task Force.
July 1-2. Switching station phone software crash affects Washington, Los Angeles, Pittsburgh, San Francisco.
September 17. AT&T phone crash affects New York City and three airports.
Introduction
This is a book about cops, and wild teenage whiz- kids, and lawyers, and hairy-eyed anarchists, and industrial technicians, and hippies, and high-tech millionaires, and game hobbyists, and computer security experts, and Secret Service agents, and grifters, and thieves.
This book is about the electronic frontier of the 1990s. It concerns activities that take place inside computers and over telephone lines.
A science fiction writer coined the useful term "cyberspace" in 1982. But the territory in question, the electronic frontier, is about a hundred and thirty years old. Cyberspace is the "place" where a telephone conversation appears to occur. Not inside your actual phone, the plastic device on your desk. Not inside the other person's phone, in some other city. *The place between* the phones. The indefinite place *out there,* where the two of you, two human beings, actually meet and communicate.
Although it is not exactly "real," "cyberspace" is a genuine place. Things happen there that have very genuine consequences. This "place" is not "real," but it is serious, it is earnest. Tens of thousands of people have dedicated their lives to it, to the public service of public communication by wire and electronics.
People have worked on this "frontier" for generations now. Some people became rich and famous from their efforts there. Some just played in it, as hobbyists. Others soberly pondered it, and wrote about it, and regulated it, and negotiated over it in international forums, and sued one another about it, in gigantic, epic court battles that lasted for years. And almost since the beginning, some people have committed crimes in this place.
But in the past twenty years, this electrical "space," which was once thin and dark and one-dimensional -- little more than a narrow speaking-tube, stretching from phone to phone -- has flung itself open like a gigantic jack-in-the- box. Light has flooded upon it, the eerie light of the glowing computer screen. This dark electric netherworld has become a vast flowering electronic landscape. Since the 1960s, the world of the telephone has cross-bred itself with computers and television, and though there is still no substance to cyberspace, nothing you can handle, it has a strange kind of physicality now. It makes good sense today to talk of cyberspace as a place all its own.
Because people live in it now. Not just a few people, not just a few technicians and eccentrics, but thousands of people, quite normal people. And not just for a little while, either, but for hours straight, over weeks, and months, and years. Cyberspace today is a "Net," a "Matrix," international in scope and growing swiftly and steadily. It's growing in size, and wealth, and political importance. People are making entire careers in modern cyberspace. Scientists and technicians, of course; they've been there for twenty years now. But increasingly, cyberspace is filling with journalists and doctors and lawyers and artists and clerks. Civil servants make their careers there now, "on-line" in vast government data- banks; and so do spies, industrial, political, and just plain snoops; and so do police, at least a few of them. And there are children living there now.
People have met there and been married there. There are entire living communities in cyberspace today; chattering, gossipping, planning, conferring and scheming, leaving one another voice-mail and electronic mail, giving one another big weightless chunks of valuable data, both legitimate and illegitimate. They busily pass one another computer software and the occasional festering computer virus.
We do not really understand how to live in cyberspace yet. We are feeling our way into it, blundering about. That is not surprising. Our lives in the physical world, the "real" world, are also far from perfect, despite a lot more practice. Human lives, real lives, are imperfect by their nature, and there are human beings in cyberspace. The way we live in cyberspace is a funhouse mirror of the way we live in the real world. We take both our advantages and our troubles with us.
This book is about trouble in cyberspace. Specifically, this book is about certain strange events in the year 1990, an unprecedented and startling year for the the growing world of computerized communications.
In 1990 there came a nationwide crackdown on illicit computer hackers, with arrests, criminal charges, one dramatic show-trial, several guilty pleas, and hu
ge confiscations of data and equipment all over the USA.
The Hacker Crackdown of 1990 was larger, better organized, more deliberate, and more resolute than any previous effort in the brave new world of computer crime. The U.S. Secret Service, private telephone security, and state and local law enforcement groups across the country all joined forces in a determined attempt to break the back of America's electronic underground. It was a fascinating effort, with very mixed results.
PART ONE: Crashing the System
On January 15, 1990, AT&T's long-distance telephone switching system crashed.
This was a strange, dire, huge event. Sixty thousand people lost their telephone service completely. During the nine long hours of frantic effort that it took to restore service, some seventy million telephone calls went uncompleted.
Losses of service, known as "outages" in the telco trade, are a known and accepted hazard of the telephone business. Hurricanes hit, and phone cables get snapped by the thousands. Earthquakes wrench through buried fiber-optic lines. Switching stations catch fire and burn to the ground. These things do happen. There are contingency plans for them, and decades of experience in dealing with them. But the Crash of January 15 was unprecedented. It was unbelievably huge, and it occurred for no apparent physical reason.
The crash started on a Monday afternoon in a single switching-station in Manhattan. But, unlike any merely physical damage, it spread and spread. Station after station across America collapsed in a chain reaction, until fully half of AT&T's network had gone haywire and the remaining half was hard-put to handle the overflow. Within nine hours, AT&T software engineers more or less understood what had caused the crash. Replicating the problem exactly, poring over software line by line, took them a couple of weeks. But because it was hard to understand technically, the full truth of the matter and its implications were not widely and thoroughly aired and explained. The root cause of the crash remained obscure, surrounded by rumor and fear.

 Mirrorshades: The Cyberpunk Anthology
Mirrorshades: The Cyberpunk Anthology The Wonderful Power of Storytelling
The Wonderful Power of Storytelling Love Is Strange (A Paranormal Romance)
Love Is Strange (A Paranormal Romance) Globalhead
Globalhead Essays. FSF Columns
Essays. FSF Columns The Hacker Crackdown
The Hacker Crackdown Bicycle Repairman
Bicycle Repairman Black Swan
Black Swan Crystal Express
Crystal Express Islands in the Net
Islands in the Net Pirate Utopia
Pirate Utopia GURPS' LABOUR LOST
GURPS' LABOUR LOST The Dead Media Notebook
The Dead Media Notebook Unstable Networks
Unstable Networks The Manifesto of January 3, 2000
The Manifesto of January 3, 2000 Heavy Weather
Heavy Weather Involution Ocean
Involution Ocean The Epic Struggle of the Internet of Things
The Epic Struggle of the Internet of Things A Good Old-Fashioned Future
A Good Old-Fashioned Future The Littlest Jackal
The Littlest Jackal Zeitgeist
Zeitgeist Totem Poles
Totem Poles Ascendancies
Ascendancies CyberView 1991
CyberView 1991 War Is Virtual Hell
War Is Virtual Hell Taklamakan
Taklamakan Holy Fire
Holy Fire Cyberpunk in the Nineties
Cyberpunk in the Nineties Schismatrix Plus
Schismatrix Plus The Artificial Kid
The Artificial Kid Essays. Catscan Columns
Essays. Catscan Columns Maneki Neko
Maneki Neko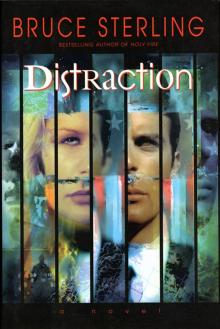 Distraction
Distraction In Paradise
In Paradise Red Star, Winter Orbit
Red Star, Winter Orbit Luciferase
Luciferase